Is your DKIM
correctly configured?
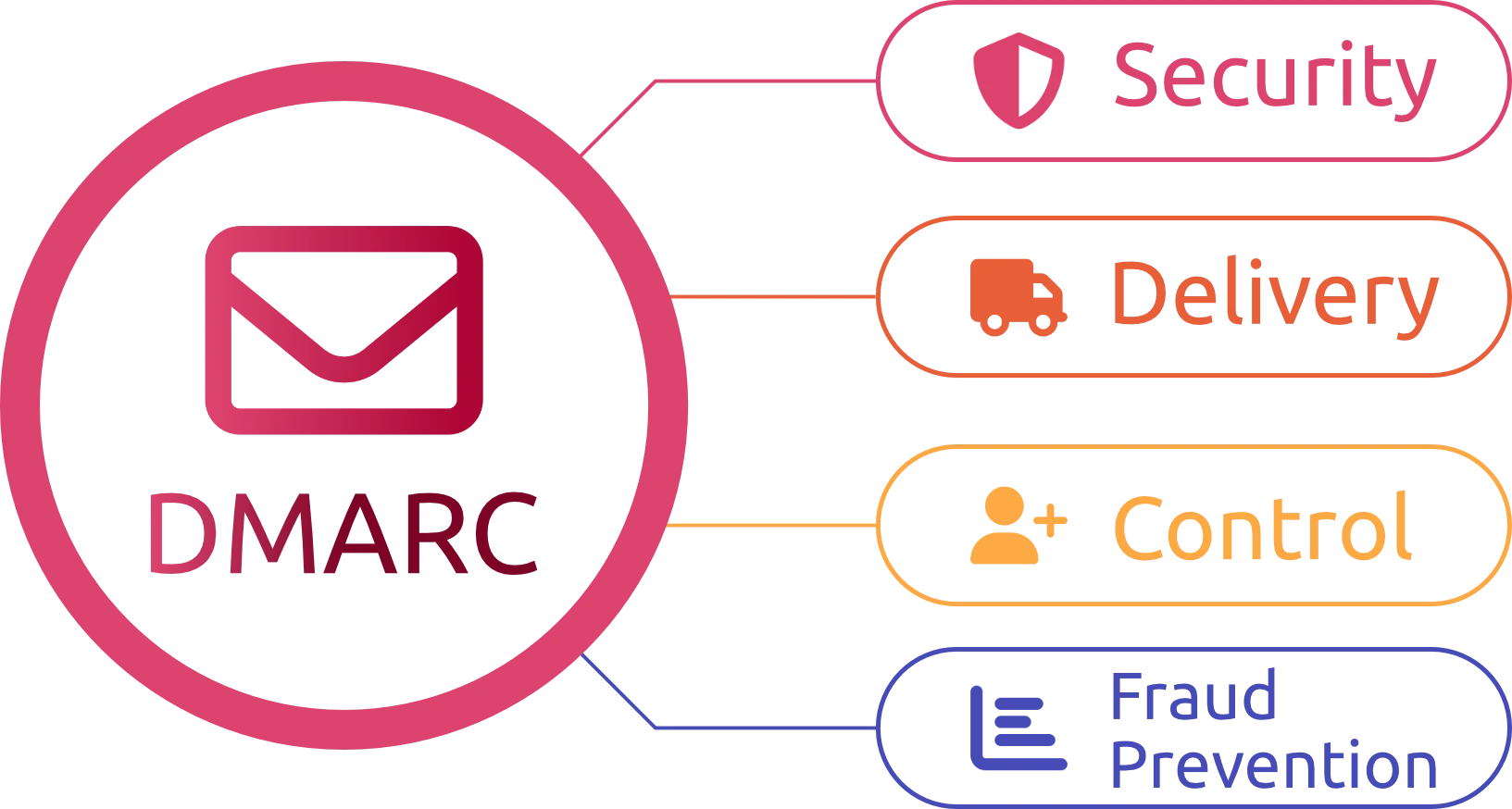
Check DKIM keys and signatures in seconds. Verify selectors, key length, and TXT records to prevent spoofing and delivery issues.
Enter your domain and (optionally) a selector to validate your DKIM setup.